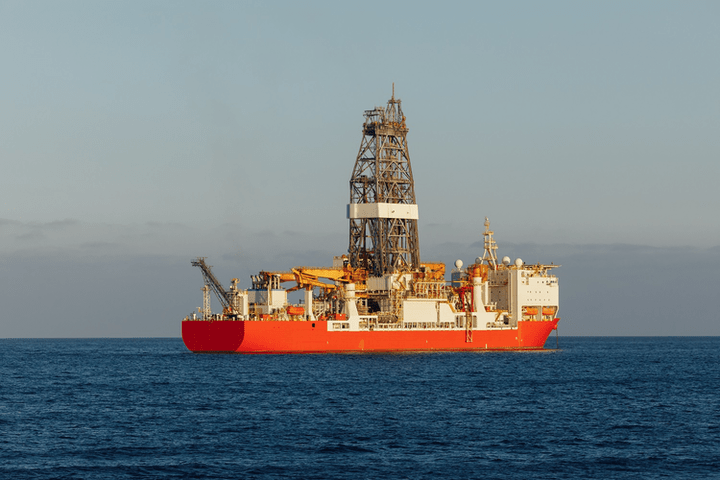
(Offshore) Cyber defense provider Naval Dome and a major international operating company have completed a joint two-year project to identify and mitigate cyber risks common to deepwater drilling rigs.
The project’s findings indicate that the minimum industry guidelines, regulations, and security techniques are out of step with current platform technology, connectivity requirements, and cyber-attack methodology. It culminated in the installation and pilot testing of Naval Dome’s Endpoint cyber defense system onboard drilling rigs in the Gulf of Mexico.
In a joint research paper presented at the Offshore Technology Conference in Houston last week, the authors stated: “Activities over two years have demonstrated shortfalls and real challenges that need to be addressed if we are to create a more cyber-secure deepwater drilling rig environment.”
During the Cyberdefence of Offshore Deepwater Drilling Rigs presentation, Adam Rizika, Head of Strategy, Naval Dome, said: “Where systems installed on offshore platforms had traditionally been isolated and unconnected, limiting cyber hack success, the increase in remote monitoring and autonomous control, IOT, and digitalization has made rigs much more susceptible to attack.”
During the project, the test rigs’ operation technology (OT) networks were penetrated using a software installation file for dynamic positioning and workstation charts. He said that the company simulated an OEM service technician unwittingly using a USB stick with malicious software containing three zero-day exploits.
“The modified file was packaged in a way that looked and acted like the original one and passed anti-virus scanning without being identified as a cyberattack or picked up by the installed cyber network traffic monitoring system,” he said.
Although the attack was carried out internally, Rizika said remote execution was feasible using the rig’s externally facing network connections.
“Penetration testing confirmed how a targeted cyber attack on a deepwater drilling rig could result in a serious process safety incident, with associated financial and reputational impact,” he said.
In the paper, the authors stated that pilot tests confirm traditional, “perimeter type” IT transplanted OT cyber security solutions, such as anti-virus, network monitoring and firewalls, are not enough to protect critical safety and processing equipment from attack. These solutions leave rigs vulnerable.
“It is abundantly clear that more advanced purpose-built solutions are needed to better protect an offshore platform from exposure to external and internal cyber attacks, whether targeted or otherwise,” Rizika said.
The paper also highlighted a shortage of OT cyber domain skilled staff; regulation and controls that are slow to evolve and be implemented; an IT-centric approached being applied to an OT environment; and a mismatch between drilling rig systems and equipment and their supporting software.
Rizika said: “Although industry guidelines and regulations offer minimum standard requirements, we found the advancement in rig technology, connectivity, and cyber-attack methodology has outpaced the regulations, driving the need for a more comprehensive approach.”
Naval Dome CEO Itai Sela said: “The project and successful pilot testing of a multi-layer cyber defense solution aboard these rigs has demonstrated that both new and legacy OEM systems can be better protected from internal and external cyberattack vectors, without the need for expensive equipment upgrades, or higher overheads that lead to an increase in total cost of ownership.”
He added: “Results to date demonstrate that the endpoint system is robust and can operate without interfering with ongoing rig operations. The cost of upgrading the obsolete systems is high, and even if upgrades are undertaken vulnerabilities can still remain.”
By approaching the problem differently, the companies said a cyber resilient environment can be accelerated onboard offshore installations.
Leave a comment